What is a Virtual Private Network? A Virtual Private Network, or VPN, is a security service that creates a secure and encrypted tunnel between the device and the internet. VPN helps in masking
What is a Virtual Private Network?
A Virtual Private Network, or VPN, is a security service that creates a secure and encrypted tunnel between the device and the internet. VPN helps in masking the IP address of the user and protects sensitive data. It also helps in securing browsers, along with allowing bypassing geo-restrictions and providing secure remote access to private networks.
The VPN works by creating a secure connection to a remote server, which is operated by the VPN provider. While using the VPN, the data passes through this tunnel, masking the original location of the users.
The virtual private network offers key benefits to users, like offering data encryption, bypassing restrictions, and securing remote work. It also hides the actual IP address and location of the user and replaces it with the location of the server of the VPN provider.
How Do Virtual Private Networks Work?
At its most fundamental level, VPN tunneling ensures a point-to-point connection that is inaccessible to unauthorized users. In order to create a tunnel, VPNs utilize tunnelling protocols over existing networks. Distinct VPNs with different tunnelling protocols like Secure Socket Tunnelling Protocol or OpenVPN. The tunneling protocol ensures encryption of data with varying strengths as per the platform utilizing VPN, like the Windows Operating System (OS) utilizing SSTP. The endpoint device must launch a VPN client (software app) in the cloud or locally. The client operates in the background and is noticeable to users unless it creates performance issues.
Typically, the search history of the user is associated with the server IP address of the VPN. VPN services leverage servers located in distinct geographical areas. By utilizing a VPN tunnel, the user device gets connected to another network. This obscures the true IP address and encrypts the data, securing private data from attackers or others looking to get access to the activities of the individuals. The tunnel links the user’s device to an exit node to a different and distant location, which makes others think that the user is accessing the network from a different location.
Virtual Private Networks can impact performance in different ways, like speed of internet connection, protocol types, and encryption types. In VPNs, poor QoS (Quality of Service), which is outside the control of IT departments, can impact the performance.
A kill switch is a security feature in a few VPNs that IT teams use as a last resort. If something disrupts the VPN connection, the kill switch disconnects the device automatically from the internet, removing the possibility of exposing your IP address.
You will generally find two types of kill switches: system-level and application-level. Application-level kill switches terminate specific applications, while system-level kill switches turn off the internet traffic should a VPN connection terminate. Kill switches utilize the following two protocols:
- Active Kill Switch Protocols: These prevent devices from linking to unsafe networks when a VPN connection is established. Apart from disruptions in the server, devices get disabled when they are not connected to the internet.
- Passive Kill Switch Protocols: These are highly secure. They prevent the devices from connecting to non-VPN connections even when they are not connected to the VPN server.
Application of Virtual Private Networks
Consistent internet users and businesses utilize VPNs for virtual privacy. Businesses implement VPNs to make sure authorized users can gain access to their data center via encrypted channels. VPNs allow users to link to a database from the same business located in different areas.
VPNs enable remote employees, business travelers, and gig economy freelance workers to access software applications that are hosted on proprietary networks. To gain access to a restricted resource via a Virtual Private Network, the user must be authorized to utilize the VPN and must pass through one or more authentication factors. These can be security tokens, passwords, or biometric data.
When an internet user surfs through the web, an attacker can gain access to data, including sensitive information like browsing history or IP addresses. If privacy becomes a main concern, having a VPN can give users peace of mind. A lot of users find great value in VPN’s encryption as they get the ability and anonymity to access content that is geographically blocked.
However, VPNs should only be used for ethical practices. They should not be used to access content that is harmful or illegal. Ethical use cases of VPNs include journalists who want to access content from another country to create news stories.
Key Protocols of Virtual Private Networks
VPN protocols ensure a relevant security level to connect with systems that cannot be matched by the core network infrastructure alone. Numerous distinct protocols can secure and encrypt data. They involve the following:
- IP Security (IP Sec)
- Transport Layer Security (TLS) and Secure Sockets Layer (SSL)
- Point-to-Point Tunnelling Protocol (PPTP)
- Layer 2 Tunneling Protocol (L2TP)
- OpenVPN
Types of Virtual Private Networks
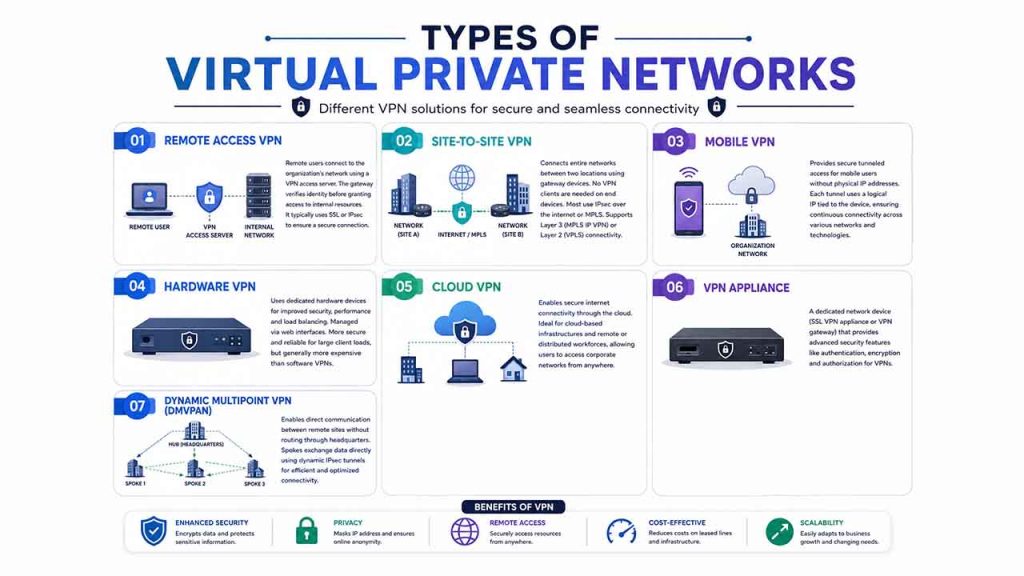
Network administrators have numerous options when it comes to implementing a VPN, including the following:
Remote Access VPN:
Remote access clients can connect with VPN access server on the network of the organization. The gateway needs the device to verify its identity before giving access to internal network resources. This type generally depends on either SSL or IPsec to make sure that the connection is secure.
Site-to-Site VPN:
A site-to-site VPN utilizes a gateway device to link an entire network in one location to a different network in another location. End-node devices existing in remote locations do not need VPN clients since the gateway manages the connection. Most site-to-site VPNs connected to the internet utilize IPsec. It is also quite common for them to utilize Multiprotocol Label Switching (MPLS) connections instead of the public internet as transport. It is possible to either have Layer 3 connectivity (MPLS IP VPN) or Layer 2 (Virtual Private Network Local Area Network Service) operating across the base transport links.
Mobile VPN:
In mobile Virtual Private Network, the network still exists at the edge of the network of the organization, allowing secure tunneled access by authorized and authenticated clients. However, mobile VPNs are not associated with physical IP addresses. Each tunnel is tied to a logical IP address instead. That logical IP address stays connected to the mobile device. An active mobile VPN ensures consistent service to the users and can transition across access technologies and numerous private and public networks.
Hardware VPN:
Hardware VPNs provide a great number of advantages over software-driven VPNs. Apart from providing improved security, hardware Virtual Private Networks can also ensure load balancing for large client loads. Web browser interfaces handle administration. A hardware VPN is more expensive than a software-based one. Because of the expense, hardware VPNs have become more feasible for larger enterprises. Numerous vendors can provide devices that can work as hardware VPNs.
Cloud VPN:
Cloud VPNs help users get a secure internet connection through the cloud. This is advantageous for businesses with cloud-driven network infrastructure or remote or distributed workforces. With the help of cloud VPN, users can gain access to corporate networks remotely, irrespective of location.
VPN Appliance:
VPN appliance, which users also call as SSL VPN appliance or VPN gateway appliance, is a network device with improved security features. It is a router that gives added authorization, protection, authentication, and encryption for VPNs.
Dynamic Multipoint Virtual Private Network (DMVPAN):
A DMVPN exchanges information between various sites without needing to go through the VPN server or router of the organization’s headquarters. A DMVPN ensures a mesh VPN service that operates on firewall concentrators and VPN routers. Every remote site has a router configured to tether with the hub of the company’s headquarters.
When two spokes are needed to exchange data between each other, for a voice-over-IP telephone call, for instance. The spoke connects with the hub, gets the required information about the other end, and ensures a dynamic IPsec tunnel between them directly.
Benefits and Challenges of Virtual Private Networks
Benefits of Virtual Private Networks
- Users have the capability to hide their browsing data and IP address.
- Encrypt the data and secure connections.
- Access the content that is geologically restricted.
- Make it tough for advertisers to target ads for individuals.
Limitations of Virtual Private Networks
- Not all devices can support VPNs.
- Even if you use VPNs, there is no guarantee that you will be secure against all threats.
- To get more reliable features, encryption, and anonymity, you will have to use paid VPNs.
- Using VPNs can reduce your overall network speed.
- Anonymity provided by the VPNs has specific limitations. For instance, browser fingerprinting is still quite possible.
Choosing the Right Virtual Private Networks?
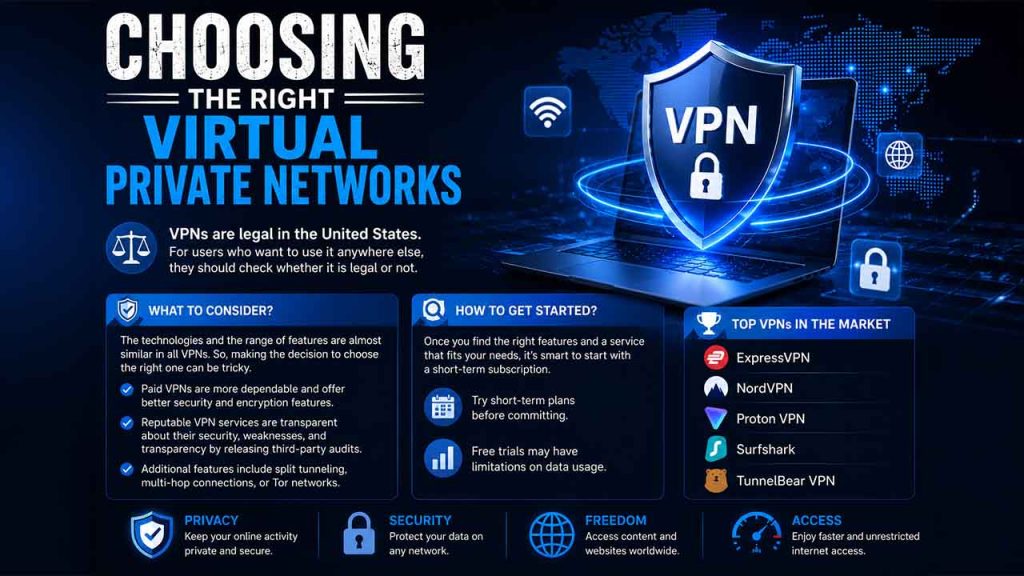
VPNs are legal in the United States. For users who want to use it anywhere else, they should check whether it is legal or not.
The technologies and the range of features are almost similar in all VPNs. So, making the decision to choose the right one can be tricky. Paid VPNs tend to be more dependable and have more security and encryption features. Reputable VPN services are honest about their strength, security, weaknesses, and transparency by releasing third-party audits. Additional features in VPN involve split tunneling, access to multi-hop connections, or Tor networks.
Once individuals find the additional features and get a service that they think will work for them, it is a nice idea to begin with a short-term subscription. A few free trial versions might involve limitations on the usage of data.
Top VPNs in the market include ExpressVPN, NordVPN, Proton VPN, SurfShark, TunnelBearVPN, etc.
Conclusion
Virtual Private Networks have become vital platforms for secure digital privacy, protecting confidential data, and accessing content that is geo-restricted. Whether you use it for personal use or business processes, selecting the right VPN depends on your particular budget, requirements, and security needs. While VPNs are not a comprehensive cybersecurity solution, they greatly minimize exposure to cyber threats. Go for a reputable and paid VPN service that can offer you robust encryption and a transparent no-logs policy for the best security.
FAQs About Virtual Private Networks (VPN)
Q1. What is a virtual private network?
A- Virtual Private Networks, or VPNs, give users a secure and encrypted connection between their device and a private server, obscuring IP address and securing data from cyber threats, ISP tracking, and third parties.
Q2. Why do I need a VPN?
A- A VPN can help you ensure online privacy, bypass geo-restrictions, secure data on public Wi-Fi, and avoid ISP tracking.
Q3. Does VPN work for Grok?
A- Yes, you can use Grok with VPN. All you have to do is connect with a nearby server, then open Grok, log in, and start using it.
Q4. Are VPNs truly anonymous?
A- No, while they obscure your IP addresses, websites can still get your data through cookies, browser fingerprinting, and user logins.
Q5. Are free VPNs safe?
A- Free VPNs are generally not considered safe since they mostly monetize data by monitoring browser habits, selling data to third parties, and displaying intrusive advertisements.
Respond to this article with emojis